Git repositories that support projects needing Docker images and containers should follow this directory standard. Any project that uses vendor tools or apps should store support data in a similar subdirectory structure. Notes here are relative to the Repository Root.
Docker Files
Composer
The Docker compose file should end up here:
./Vendors/Docker/Composers
This is for files the build and launch containers.
Images
This is for stuff that builds images used to launch custom containers.
The files that support building images should end up here:
./Vendors/Docker/Images
Dockerfile or Dockerfile-openclaw may live here.
Supporting files for building images go in these directories:
./Vendors/Docker/Images/Files
For files that are put in the SLP SaaS repo that support image building, public files.
This often contains subdirectories for files to copy from the host (stored in the SLP_SaaS repo) to the guest.
For example:
./apache/sites-avaiable/000-default.conf – for a Docker container with Apache websites
./php/docker-php-ext-redix.ini – for a Docker container with PHP and Redis support
./ssl/_wildcard.storelocatorplus.com+2.pem – for an SSL cert
Things in Files/* in this Docker folder are often copied via Dockerfile to build the image
./Vendors/Docker/Images/Secrets
It can contains supporting secret files that do not get commited to the repo.
For example: do-not-commit-codebuild-vars.env
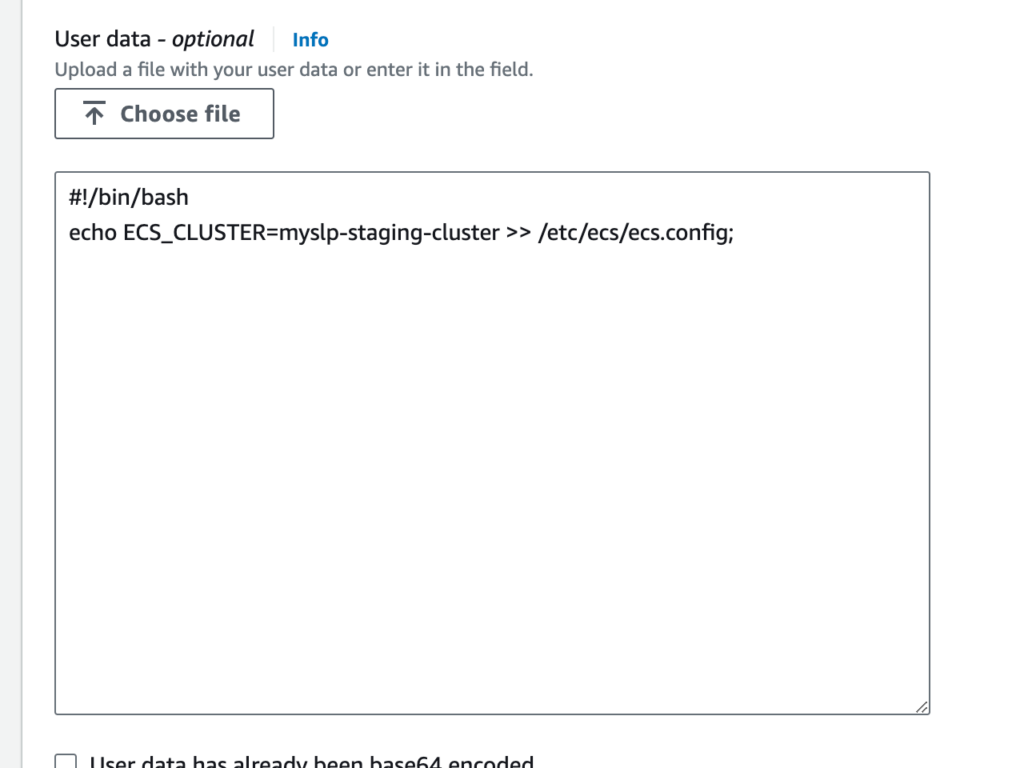
This is for environment variables needed for Code Build on AWS with values set like AWS_DEFAULT_REGION=us-east-1
The README instructions would say something like “copy ./Images/Secrets-Examples/codebuild-vars.env to ./Images/Secrets/do-not-commit-codebuild-vars.env
SLP_SaaS_Docker_Directory_Standard.md
# SLP SaaS — Docker Directory Standard
This document captures the current **directory layout conventions** for Docker-related assets used with the **SLP SaaS** project, as described by Lance.
## Project roots (MBP)
- **SLP SaaS repo root**
- `/Users/lancecleveland/phpStorm Projects/SLP_SaaS`
- **Testing area (under SLP_SaaS)**
- `/Users/lancecleveland/phpStorm Projects/SLP_SaaS/Testing/`
- **myslp-cypress repo (local checkout)**
- `/Users/lancecleveland/phpStorm Projects/SLP_SaaS/Testing/myslp-cypress`
## Canonical Docker directory structure (within myslp-cypress)
All Docker-related standards below are relative to:
- `/Users/lancecleveland/phpStorm Projects/SLP_SaaS/Testing/myslp-cypress/Vendors/Docker/`
### 1) Compose files
**Docker Compose files** should live here:
- `Vendors/Docker/Composers/`
Example (full path):
- `/Users/lancecleveland/phpStorm Projects/SLP_SaaS/Testing/myslp-cypress/Vendors/Docker/Composers`
Notes:
- This is the standard landing zone for any new compose setup (e.g., an E2E Eddie/OpenClaw + Cypress compose).
### 2) Image build definitions
**Files that support building images** should live here:
- `Vendors/Docker/Images/`
Example (full path):
- `/Users/lancecleveland/phpStorm Projects/SLP_SaaS/Testing/myslp-cypress/Vendors/Docker/Images`
Notes:
- Dockerfiles may live here, including variants like `Dockerfile` or `Dockerfile-openclaw`.
### 3) Public build-support files (committed)
**Supporting files used during image builds** (intended to be committed) should live here:
- `Vendors/Docker/Images/Files/`
Example (full path):
- `/Users/lancecleveland/phpStorm Projects/SLP_SaaS/Testing/myslp-cypress/Vendors/Docker/Images/Files`
Conventions:
- This directory often contains subdirectories that mirror container filesystem targets.
- Contents are typically copied into an image via `Dockerfile` using `COPY ...`.
Examples of typical contents:
- `./apache/sites-available/000-default.conf` — Apache site config
- `./php/docker-php-ext-redix.ini` — PHP extension/config file (example)
- `./ssl/_wildcard.storelocatorplus.com+2.pem` — SSL cert material (example)
### 4) Secrets (NOT committed)
**Supporting secret files** (not committed to the repo) should live here:
- `Vendors/Docker/Images/Secrets/`
Example (full path):
- `/Users/lancecleveland/phpStorm Projects/SLP_SaaS/Testing/myslp-cypress/Vendors/Docker/Images/Secrets`
Conventions:
- This may contain env var files or other sensitive build/runtime inputs.
- Example secret file:
- `do-not-commit-codebuild-vars.env`
Example usage pattern to document in READMEs:
- “Copy `./Images/Secrets-Examples/codebuild-vars.env` to `./Images/Secrets/do-not-commit-codebuild-vars.env` and edit values (e.g., `AWS_DEFAULT_REGION=us-east-1`).”
### 5) Secrets examples (committed templates)
**Example secret files** (templates that *are* committed) should live here:
- `Vendors/Docker/Images/Secrets-Examples/`
Example (full path):
- `/Users/lancecleveland/phpStorm Projects/SLP_SaaS/Testing/myslp-cypress/Vendors/Docker/Images/Secrets-Examples`
Purpose:
- Provide safe-to-commit starter files that developers can copy into `Secrets/`.
## Recommended README conventions (optional)
When adding a new compose or image:
- Put the compose YAML in `Vendors/Docker/Composers/`.
- Put the Dockerfile(s) in `Vendors/Docker/Images/`.
- Put committed build inputs in `Vendors/Docker/Images/Files/`.
- Put local-only secrets in `Vendors/Docker/Images/Secrets/`.
- Put example secrets in `Vendors/Docker/Images/Secrets-Examples/`.
## Source
Captured from Lance Cleveland’s notes in Slack (2026-03-21).